The Global Scholarly Directory.
Discover world-class academic programs curated for the modern intellectual. Search through 19877+ degrees and professional certificates.
 Sungkyunkwan University
Sungkyunkwan University
The Korean Alphabet: An Introduction to Hangeul
This course introduces Korean characters,'Hangeul', and provides high-level knowledge related to Hangeul. In this course, the background of 'Hangul' is created, who made the Hangeul, and according to what principle it is systematically explained. It also introduces anecdotes related to Korean tourist destinations related to Hangeul and teaches how to write Hangeul. Learners can increase their understanding of Korea, learn Hangeul accurately, and cultivate high-level knowledge of Hangeul.
 Google Cloud
Google Cloud
Looker Functions and Operators
This is a Google Cloud Self-Paced Lab. In this lab, you will learn how to use Looker to pivot dimensions, reorder columns, remove fields, and use table calculations.
 Arizona State University
Arizona State University
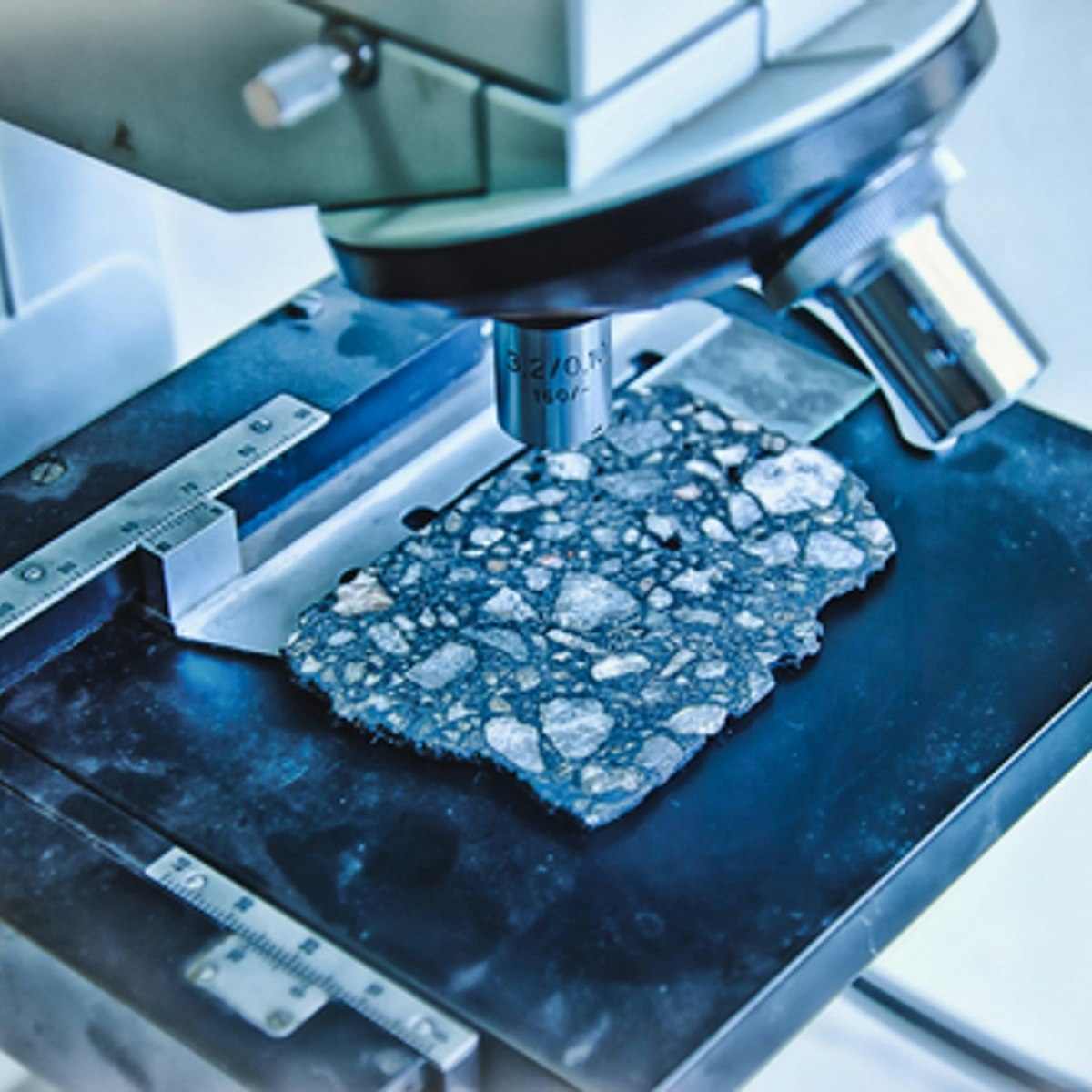
Shape and Property Control of Metals I & II
This course introduces students to the basic concepts of shaping materials and their impacts on properties and structure. An introduction to the fundamentals of diffusion in a solid follows. We present different types of diffusion mechanisms and their dependence on temperature. The role of dislocation on mechanical properties and how it can be used to strengthen materials will be shown.
 Columbia University
Columbia University
Causal Inference
This course offers a rigorous mathematical survey of causal inference at the Master’s level. Inferences about causation are of great importance in science, medicine, policy, and business. This course provides an introduction to the statistical literature on causal inference that has emerged in the last 35-40 years and that has revolutionized the way in which statisticians and applied researchers in many disciplines use data to make inferences about causal relationships. We will study methods for collecting data to estimate causal relationships. Students will learn how to distinguish between relationships that are causal and non-causal; this is not always obvious. We shall then study and evaluate the various methods students can use — such as matching, sub-classification on the propensity score, inverse probability of treatment weighting, and machine learning — to estimate a variety of effects — such as the average treatment effect and the effect of treatment on the treated. At the end, we discuss methods for evaluating some of the assumptions we have made, and we offer a look forward to the extensions we take up in the sequel to this course.
 Coursera
Coursera
Analyze, Create, and Evaluate Cloud Security
Master the critical skills for securing cloud infrastructure through systematic analysis, proactive policy creation, and comprehensive compliance evaluation. This course empowers you to become a guardian of cloud security by teaching you to detect suspicious privilege escalations in IAM audit logs, automate security governance through infrastructure-as-code policies, and assess organizational controls against industry standards like SOC 2 and NIST. This Short Course was created to help Machine Learning and Artificial Intelligence professionals accomplish robust cloud security governance that scales with enterprise demands. By completing this course, you'll be able to investigate security incidents with precision, prevent vulnerabilities through automated policy enforcement, and demonstrate compliance readiness that builds stakeholder confidence. By the end of this course, you will be able to: • Analyze IAM audit logs to detect anomalous privilege escalations • Create infrastructure-as-code policies to enforce encryption and network segmentation • Evaluate security controls and practices against industry standards and compliance requirements This course is unique because it bridges the gap between security theory and practical implementation, teaching you to think like both a security investigator and a proactive system architect. To be successful in this project, you should have a background in cloud infrastructure, basic security concepts, and familiarity with Infrastructure-as-Code tools.

